- AI ·

The Beeders White Label Tokenization Platform offers a seamless web dApp UX with a user-friendly interface that ensures a smooth user experience. The admin panel is also intuitive and easy to use, providing an efficient way to manage the platform and its users.
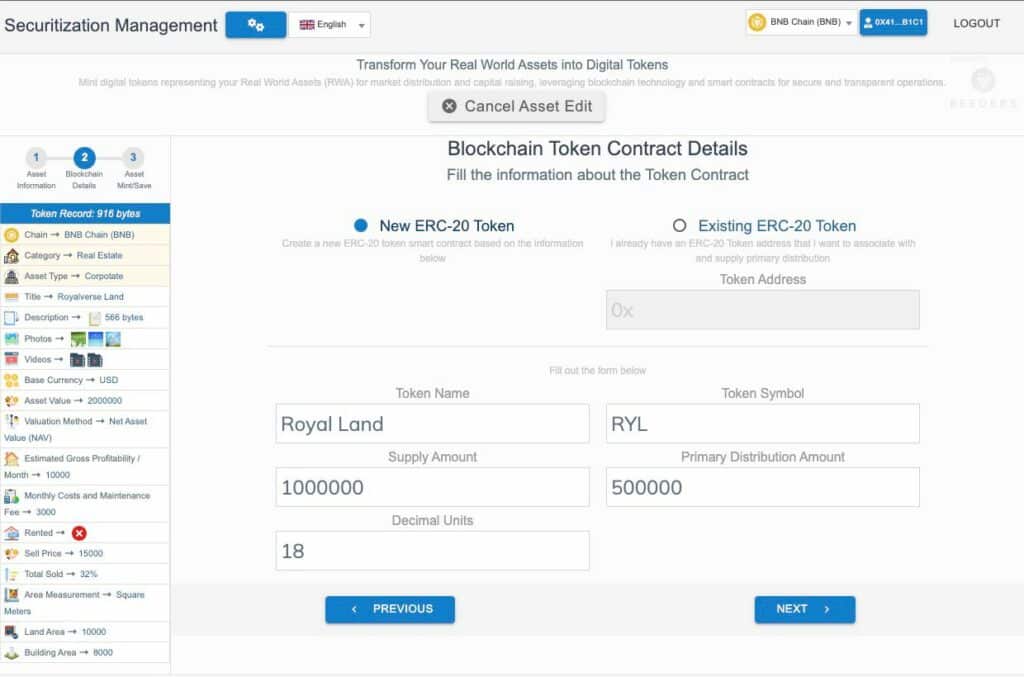
Creating and issuing tokens on the platform is straightforward and can be done quickly. The platform supports a variety of token standards, including security tokens, enabling users to conduct token offers as STOs (Security Token Offerings) with ease.
To make the process of purchasing tokens as convenient as possible, the platform supports transactions through BTC, ETH, and other popular cryptocurrencies. Multi-language and multi-currency support further expands the platform’s reach and ensures that users from around the world can participate in token offerings.
Security is of the utmost importance on the Beeders White Label Tokenization Platform, and the team has implemented robust security measures to protect user data and funds. The platform also undergoes regular security audits to ensure that it remains secure and reliable.
Overall, the Beeders White Label Tokenization Platform offers a comprehensive solution for businesses looking to tokenize their assets or launch a token offering. With its user-friendly interface, support for multiple languages and currencies, and top-notch security, the platform is a reliable and efficient choice for any tokenization project.
BEEDERS Tokenization Platform is designed to cater to a wide range of businesses, from individual entrepreneurs who want to tokenize their physical or digital assets, to large corporations, real estate developments, family offices, and venture capital firms looking to securitize their assets through tokenization. The platform is ideal for:
At its core, our platform is a white-label solution, serving as a Software-as-a-Service infrastructure to enable the tokenization of real-world assets.
Whether you wish to utilize the platform to tokenize for your own purposes, or to offer tokenization services to your clientele, BEEDERS Web3 SaaS is tailored to fulfill your needs. Explore the opportunities, enhance your business growth and give your organization a competitive edge with asset tokenization.
Don’t wait – start your tokenization journey with us today!
The Beeders White Label Tokenization Platform is a blockchain-based solution that supports various token standards. The platform utilizes Ethereum Smart Contracts and is compatible with ERC20 and ERC1400 standards, among others. This allows for seamless integration with existing Ethereum-based projects.
Additionally, the Beeders White Label Tokenization Platform supports other protocols, such as Hyperledger, Solana, among others. This level of adaptability ensures that the platform can be tailored to meet the specific needs of each client and enables easy integration with various blockchain networks.
The platform’s compatibility with multiple protocols enables businesses to streamline their tokenization process and simplify their operations. Whether you are looking to launch a security token offering, tokenize your assets, or create a new cryptocurrency, the Beeders White Label Tokenization Platform can help you achieve your goals efficiently and effectively.
By utilizing various blockchain protocols, the Beeders White Label Tokenization Platform offers a versatile solution that can cater to a wide range of businesses and industries. Its adaptability and compatibility with multiple standards make it an ideal choice for any blockchain-based tokenization project.
The Beeders White Label Tokenization Platform provides technical support for businesses to launch compliant token offerings, featuring KYC/AML checks and compliance tools. While offering regulatory guidance, the responsibility for adhering to local laws rests with the customer.
Tokenization Core Features:
– Token Issuing (ERC20 compatible)
– Blockchain Support for Ethereum, Polygon, BNB Chain, Avalanche, and Fantom
– DEX/Swap integration
– OnChain Decentralized Data Storage
– Gas Fee Optimization
– Transaction capabilities on both Mainnet and Testnet
– Noncustodial Software Platform
Securitization:
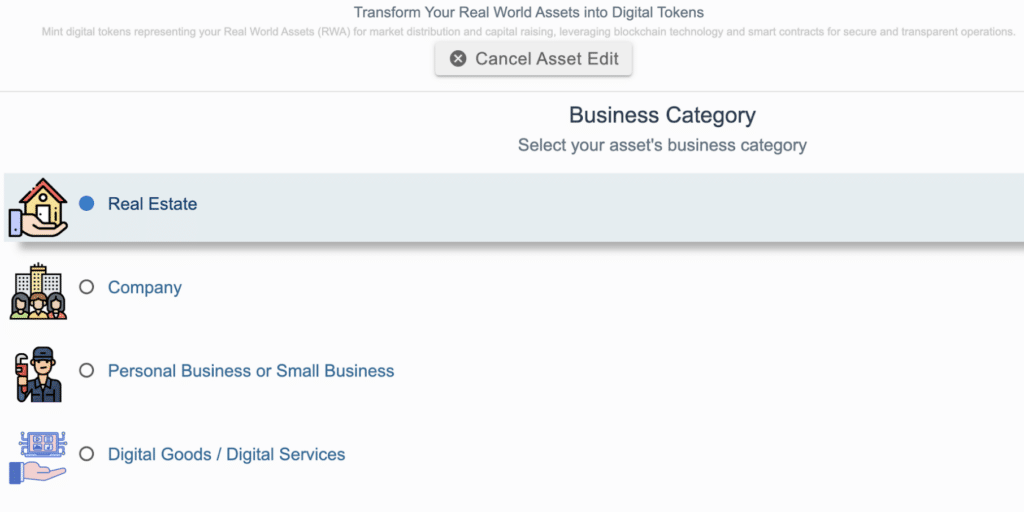
– Business Accelerator templates for various sectors including Real Estate, Companies, Personal or Small Business, and Digital Goods or Services
– Primary Distribution and Secondary Market options
– Comprehensive Documentation Management
– Token Backed Configuration
– Whitelisting
– Transfer Restrictions
– KYC/AML third-party integration
– Cap Table third-party integration
Environment:
– User-friendly Admin Panel
– Efficient Content Management
– Front-end Management
– Secure, Isolated Environment
– Multi-language support
– User Account functionality
– White label system
Additionally, we offer customized solutions to suit your specific needs, such as:
– Deflationary Protocol
– Airdrop System
– Farming
– Liquidity
– Staking
Beeders Security System
These are the terms of use, guidelines, and standard provisions for using the software-as-a-service delivered by Beeders.
Understanding of Our Role:
Beeders provides a non-custodial software/hardware wallet platform, implying that it is not a centralized software solution. It is essential to understand that as Beeders delivers this Web3 SaaS platform, it is not perceived as an operator or collaborator in the client’s business activities. Consequently, our responsibility is confined to delivering technical services and maintaining the stability and functionality of our platform.
Data Management:
Our platform stores all data on-chain, using the blockchain selected for token issuance. Compliance with regulatory obligations necessitates all users of the Beeders platform to successfully complete the KYC (Know Your Customer) process through third-party integration and adhere to our on-chain data storage policies.
Regulatory Compliance:
Beeders adheres to all stipulations and benchmarks set forth by pertinent regulatory bodies in the territory and country where our platform functions.
Prohibited Activities:
The use of Beeders software platforms for any illegal activities, including but not limited to financial pyramid schemes, money laundering, or the financing of drug and arms trafficking, is strictly forbidden. As part of our commitment to compliance, we routinely provide business information to relevant regulatory bodies.
Points to Note:
Breach of any of the rules stated above will lead to immediate service termination.
The conditions and rules set forth in this document may be altered without prior notification.
User Compliance and Platform Adaptability
Supplementary Terms of Use:
Our customers, being users of the Beeders platform, are required to strictly comply with all applicable criteria and regulations during their tokenization period, identified as securitization. They are obligated to adhere to each respective guideline corresponding to their operational location and jurisdiction.
The Beeders Web3 SaaS platform exhibits comprehensive flexibility to conform to any prevailing or prospective regulatory guidelines. The Beeders team remains fully committed and available to accommodate both broad and specific needs through requests directed to our customer support department.
The seamless operation of your activities within the Beeders platform is a consequence of your compliance and our platform’s agility in meeting your unique requirements. We fervently encourage the maintenance of a proactive communication channel with our customer support for addressing your concerns or requests.
As a Legal Office, safeguarding your clients’ assets is paramount. That’s why we’re excited to offer cutting-edge tokenization services that provide unparalleled protection. By digitizing assets into tokens, we’re able to offer an extra layer of security that traditional methods simply can’t match. With our tokenization services, your clients can rest easy knowing their assets are safe and secure.
As an Asset Investor, you understand the importance of staying ahead of the curve. That’s why we’re proud to offer a game-changing service that will revolutionize the way you do business. Our tokenization services allow you to digitize your assets into easily tradable tokens, giving you a competitive edge in today’s fast-paced market. With our help, you can expand your reach, increase liquidity, and make smarter investment decisions than ever before.
Attention all Entrepreneurs! The asset tokenization market is brimming with untapped potential, and we’re here to help you take advantage of it. As a forward-thinking business owner, you understand the importance of staying ahead of the curve. That’s why our cutting-edge tokenization services are the perfect tool to help you do just that. With our help, you can unlock new revenue streams, reduce risk, and gain a competitive edge in today’s dynamic marketplace. Don’t miss out on this exciting opportunity – get in touch with us today!
Experience the endless possibilities of asset tokenization!
Our service offers a range of use cases that can transform the way you do business, including:
Real Estate and Properties: own a fraction of a property through issued tokens.
Securities and Contracts: quantify your value and match it with the issuance of tokens.
Projects, New Businesses, Arts, and More: make tangible investments through the issuance and offer of tokens.
Companies: offer partial or total fractions of shares in tokens to unlock new investment opportunities.
Loyalty Systems: transform the way you reward and incentivize customers with our tokenization service.






